How Claspt protects your data — no black boxes.
No black boxes. No "trust us." Here is exactly how your vault is secured, what's encrypted, what isn't, and why.

Key derivation hierarchy
Two independent paths protect your vault. Your master password derives a key that encrypts the master key. The master key encrypts each individual secret block with its own unique nonce.
Cryptographic specifications
Every cryptographic decision, documented. No proprietary algorithms, no novel cryptography — only battle-tested primitives.
| Parameter | Value | Notes |
|---|---|---|
| Cipher | AES-256-GCM | Authenticated encryption — integrity and confidentiality in a single pass |
| Key derivation | Argon2id | 64 MB memory, 3 iterations, 4 parallel lanes. Resistant to GPU and ASIC attacks |
| Nonce | 96-bit random | Unique per secret block, generated via CSPRNG. Never reused |
| Master key | 256-bit | Generated via ring::rand::SystemRandom — OS-level CSPRNG |
| Implementation | ring crate | Rust bindings to BoringSSL. FIPS-validated primitives, constant-time operations |
| Memory safety | zeroize crate | All key material zeroed from memory after use. Compiler cannot optimize it away |
| Biometric storage | OS Keychain | macOS Keychain, Windows Credential Manager, Linux Secret Service API |
Claspt uses no proprietary or novel cryptography. Every primitive is a well-audited, widely deployed standard. We do not invent cryptographic algorithms — we compose them correctly.
What happens if someone
gets your files?
We assume the worst: an attacker has read access to your entire vault directory but does not have your master password.

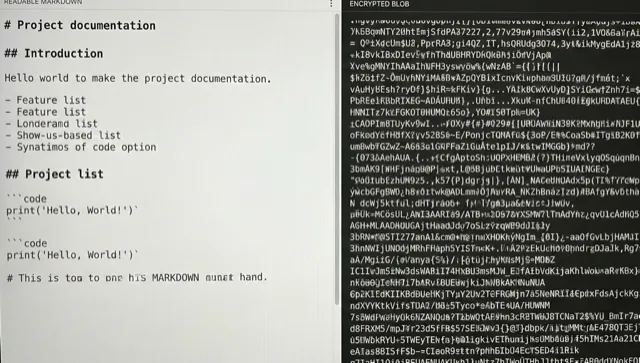
What they see
- Markdown files with your notes in plaintext
- Encrypted blobs where secret blocks are stored
- Page titles and file names
- Secret block labels (e.g., "Work VPN")
- YAML frontmatter metadata
What they cannot do
- Decrypt any secret block content without the master key
- Recover the master key from the encrypted vault.key file
- Brute-force Argon2id — 64 MB per attempt makes GPU farms impractical
- Tamper with encrypted blocks undetected — GCM authentication catches it
- Reuse nonces to weaken encryption — every block has a unique 96-bit nonce
What's encrypted vs. what's not
Claspt is deliberately transparent about what is and isn't encrypted. This is a design decision, not a limitation — and here's exactly why.
Encrypted
Passwords, API keys, card numbers, notes inside secret blocks
Encrypted at rest using your password-derived key
Auto-cleared after 30 seconds — never persisted to disk
All key material zeroed after use via the zeroize crate
Plaintext
So you can browse your vault and files are human-readable
Standard filesystem paths — works with any file manager
e.g., "Work VPN" — helps you find secrets without decrypting all of them
Tags, dates, and frontmatter — enables search and organization
Why not encrypt everything?
Full-vault encryption sounds more secure, but it trades real usability for marginal gains. Here's why Claspt takes a selective approach.
Portability
Your vault is a folder of markdown files. If Claspt disappears tomorrow, you still have every note. Full encryption makes your data hostage to the app.
Meaningful diffs
Git can show you exactly what changed in each commit — because notes are plaintext. With full encryption, every save looks like a completely different file.
Full-text search
Searching encrypted data requires decrypting everything into memory first. With plaintext notes, tantivy indexes your content and returns results in under 100ms.
Selective security
Most notes don't need encryption — your meeting notes, to-do lists, and project plans aren't secrets. Encrypting only sensitive data means you can choose what matters.
No all-or-nothing
Full-vault encryption means one wrong password attempt and you're locked out of everything. Claspt's model means you always have access to your notes — only secrets require the key.
Your secrets deserve
real encryption.
AES-256-GCM. Argon2id. Unique nonces. Memory zeroing. No telemetry, no cloud dependency, no trust required. Download Claspt and verify it yourself.